Millions of international visitors will rely on public Wi-Fi across host cities, venues, fan zones, airports, transit hubs, and hotels during the 2026 FIFA World Cup - and while connectivity will be widespread, including 5G and high-speed fiber in select locations, the security of those networks will vary considerably. Open or poorly-configured networks create measurable exposure to data theft, account compromise, and malicious interception. For travelers carrying smartphones loaded with payment credentials, booking confirmations, and personal identification, the risk is not theoretical.
Why Public Wi-Fi Remains a Persistent Security Weak Point
The core problem with public Wi-Fi is structural. Networks designed for high-volume, frictionless access are rarely optimized for security. Many lack encryption entirely. Others use outdated security protocols - WPA2, for instance, remains the dominant standard across the majority of global Wi-Fi deployments, and while it is broadly functional, it carries known vulnerabilities that attackers within network range can potentially exploit if the configuration is weak or unpatched. Only a small fraction of networks have migrated to WPA3, the current generation standard with stronger encryption and better resistance to brute-force attacks.
Beyond protocol weaknesses, public networks concentrate risk in ways that private networks do not. When thousands of people connect to the same infrastructure in a short window, the volume of data flowing across that network becomes an attractive target. Attackers do not need sophisticated tools to intercept unencrypted traffic - packet-sniffing software is freely available and requires minimal technical knowledge to operate.
The Threat of Fake Networks and Rogue Hotspots
One of the more technically straightforward and underappreciated threats in high-density environments is the rogue access point - sometimes called an evil twin attack. A malicious actor sets up a portable hotspot that mimics the name of a legitimate network, typically with minor variations. A device that has previously connected to "Airport_Free_WiFi" may automatically attempt to reconnect to any network broadcasting that same identifier, including a fake one.
Attackers can accelerate this process using deauthentication techniques that briefly disconnect devices from legitimate networks, prompting them to seek a new connection. Once a device joins a rogue network, the operator can monitor unencrypted communications, redirect users to fraudulent login pages, or capture credentials entered into what appears to be a normal web session. Travelers entering email addresses, passwords, or government ID numbers into a fake Wi-Fi portal may have no immediate indication that anything is wrong.
Warning signs worth knowing:
- Duplicate or near-identical network names in the same location - for example, a legitimate "Hotel_Guest" network alongside an unsolicited "Hotel_Guest_Free"
- Networks requiring no password, which typically means traffic is unencrypted
- Login portals that request sensitive information beyond a room number or acceptance of terms - particularly email addresses, credit card numbers, or national ID details
Practical Measures That Meaningfully Reduce Exposure
The most effective single step is avoiding public Wi-Fi for sensitive activities altogether. Mobile data - accessed through a local SIM or an eSIM configured for the host country - routes traffic through carrier infrastructure rather than venue or accommodation networks, which eliminates much of the public Wi-Fi threat surface. For international travelers, an eSIM offers a practical way to obtain local data access without waiting for a physical SIM card, often at lower cost than roaming plans.
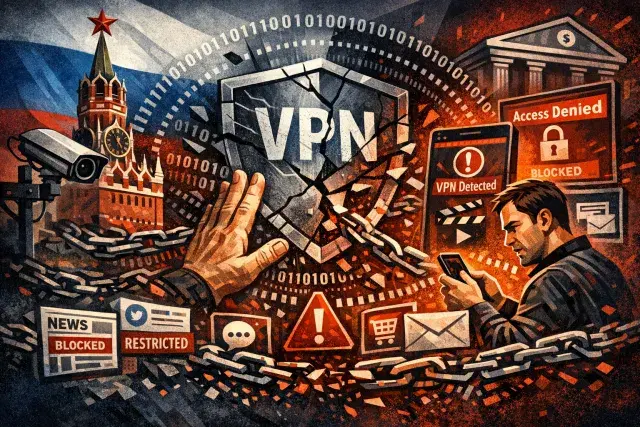
When public Wi-Fi is unavoidable, a virtual private network (VPN) provides meaningful protection. A VPN encrypts outbound traffic between a device and a remote server, making it significantly harder for anyone on the same local network to read or manipulate that data. The encryption does add some latency, but connecting to a server in or near the host country minimizes the performance impact. A VPN does not guarantee complete security - it cannot protect against threats on the destination server itself - but it substantially raises the cost and complexity of local interception.
Several additional habits reduce risk without requiring technical knowledge:
- Disable auto-connect and file-sharing before arriving in public spaces
- Remove saved public networks from your device after use to prevent automatic reconnection
- Verify the correct network name with staff or official signage before connecting
- Confirm that websites handling sensitive data show "https://" in the address bar - a padlock icon in the browser indicates an encrypted connection
- Keep device operating systems updated; security patches address known vulnerabilities that attackers actively exploit
- Use antivirus software capable of flagging suspicious networks and blocking malicious links
Context and Broader Implications for Large-Scale Public Events
The cybersecurity risks associated with large public gatherings are not new, and the World Cup is not unique in presenting them. Major international events have historically attracted not only tourists but also opportunistic cybercriminals who follow concentrations of people carrying high-value devices and credentials. What changes with an event of this scale is the density of exposure: a single compromised network in a busy transit hub can affect thousands of users over the course of a day.
Venue operators and telecommunications providers deploying event infrastructure bear responsibility for the security of networks under their control. But the architecture of public Wi-Fi - particularly in high-volume environments where guest isolation, encryption standards, and network monitoring may be inconsistently applied - means that individual vigilance remains the most reliable line of defense. Treating any public network as potentially hostile, and acting accordingly, is not excessive caution. It is the appropriate baseline.